Aws vpn wont connect your step by step troubleshooting guide: Get Back Online Fast with Proven Fixes


Aws vpn wont connect your step by step troubleshooting guide – quick facts first: many VPN connection issues with AWS VPN come down to authentication, routing, or firewall rules. If your VPN won’t connect, you’re not alone, and there’s a clear path to get back online. Today you’ll get a practical, step-by-step guide that covers the most common culprits and fixes, plus extra tips to prevent future disconnects. Here’s a compact overview of what you’ll learn:
- Quick-start checklists to verify basic connectivity
- Step-by-step troubleshooting for tunnel establishment errors
- Configuration tips for both AWS VPN Gateway and Client VPN
- Networking best practices to avoid common pitfalls
- How to test and validate successful connections
Useful resources you might want to keep handy text, not clickable: Amazon Web Services Docs - aws.amazon.com OpenVPN Community - openvpn.net IP routing basics - en.wikipedia.org/wiki/Routing NAT traversal tips - en.wikipedia.org/wiki/Network_address_translation VPN error codes and logs - stackoverflow.com
Understanding AWS VPN: What Could Be Going Wrong?
Before you jump into fixes, it helps to know the usual suspects:
- Authentication failures: wrong certificates, expired keys, or mismatched pre-shared keys PSK.
- Phase 1/Phase 2 mismatch: IKE negotiation issues, cipher suite incompatibilities.
- Routing problems: missing routes to the VPN network or incorrect CIDR.
- Firewall or security group rules: traffic blocked on specific ports or IPs.
- Client-side issues: misconfigured client software, DNS leaks, or local network restrictions.
Statistics you can use to gauge scope:
- Around 40% of AWS VPN issues are caused by misconfigured IPsec/IKE settings.
- VPNs fail to connect most often due to firewall rules on the client side or at the edge of the VPC.
- When tunnels come up but traffic doesn’t route, routing tables and security groups are usually the culprit.
Quick Start: 5-Minute Pre-Check
If you’re short on time, try this fast pass to rule out obvious blockers:
- Verify AWS VPN gateway status: ensure both tunnels are up in the AWS Console.
- Confirm client configuration matches the AWS side exactly peer ID, PSK, IKE policy.
- Check that your local firewall isn’t blocking UDP ports 500 and 4500 common IKE and NAT-T ports.
- Validate your NIC’s IP routing: does the client have a route to the VPN subnet?
- Reboot the VPN client and retry a fresh connection.
If you pass the quick checks but still see issues, move to the step-by-step fixes below.
Step-by-Step Troubleshooting Guide
1 Confirm Tunnel Status and Logs
- Check AWS VPN Connection
status: UP or DOWN? - Look at the CloudWatch logs or VPN logs for common errors: IKE_SA_INIT failed, no proposal chosen, or PSK authentication failed.
- Enable detailed logging on the client side if available.
What to do: Бесплатный vpn для microsoft edge полное руководств: Быстрое, безопасное и простое решение для серфинга
- If Tunnel 1 or Tunnel 2 is DOWN, focus on IKE phase: ensure IKE version IKEv1 vs IKEv2 and encryption algorithms match on both ends.
- If logs show PSK mismatch, reconfigure the PSK on both client and server to be identical.
2 Validate Pre-Shared Key PSK and Certificate Creds
- PSK: Make sure there are no stray spaces or line breaks when copying.
- Certificate-based auth: Ensure CA certificate, client cert, and private key are correctly installed and not expired.
- Compare fingerprints: MD5/SHA-1 fingerprints on both sides to ensure they match.
What to do:
- Regenerate PSK or reissue certificates if you suspect a mismatch or expiry.
- Re-import certificates and restart the VPN service.
3 Check IKE Phase 1 IKE_POLICY and Phase 2 IPSec Proposals
- Match encryption, integrity SHA-256, SHA-1, and DH groups Modp1024, Modp2048, ecp256 on both sides.
- Ensure the same lifetime e.g., 28800 seconds for IKE, 3600 seconds for IPSec.
What to do:
- If AWS uses AES-256 with SHA-2 and you’re on a different set, adjust client or AWS policy to match.
- For Windows clients, edit the VPN connection properties to explicitly set the IKE and IPSec proposals.
4 Inspect Routing and CIDR Configuration
- Check that your VPC CIDR and VPN subnet don’t overlap with your on-premises network.
- Ensure correct static routes exist for the VPN tunnel in the route tables.
- Confirm that there’s a path for return traffic no asymmetric routing issues.
What to do:
- Add missing routes to route tables VRF or VPC route table, depending on setup.
- If using dynamic routing BGP, confirm neighbor settings and ASNs.
5 Firewall and Security Group Rules
- On the client side: UDP ports 500 and 4500 must be allowed outbound.
- On the AWS side: Security Groups and Network ACLs must permit VPN traffic to and from the VPN client subnet and the VPC CIDR.
- Check for NAT traversal NAT-T being enabled if your gateway is behind NAT.
What to do:
- Temporarily disable local firewalls to test connectivity.
- Adjust SG/NACL rules to allow VPN traffic.
6 NAT and Private IP Address Handling
- If NAT is used between client and VPN, ensure the NAT rule doesn’t translate the VPN IPs in a way that breaks IPsec.
- Verify that the VPN client receives a correct private IP from the VPN pool.
What to do: Setting up intune per app vpn with globalprotect for secure remote access and related configurations
- Disable NAT for VPN traffic if possible and re-test.
- Confirm correct IP allocation from DHCP or VPN pool.
7 Client Software and OS-Specific Tweaks
- Windows: ensure the VPN adapter uses the correct DNS servers and that the tunnel is set to connect automatically if needed.
- macOS/Linux: confirm ipsec-tools or strongSwan config matches the AWS gateway policies.
- Ensure there are no conflicting VPN profiles.
What to do:
- Recreate the VPN profile with fresh configuration data from AWS.
- Update VPN client software to the latest version.
8 Time and Timezone Sync
- Certificate-based auth can fail if clocks are skewed.
- NTP drift can cause negotiation timeouts.
What to do:
- Enable reliable NTP synchronization on both client and server.
- Check system time to ensure it’s within a few minutes of real time.
9 DNS and Split-Tunnel Considerations
- If you’re unable to reach internal resources by name, verify DNS settings.
- For split-tunnel setups, ensure the VPN client routes only the intended subnets to avoid leaks or misrouting.
What to do:
- Point DNS to the internal resolver if needed.
- Review split-tunnel configuration and adjust routes accordingly.
10 Recreate the VPN Connection
When all else fails, a clean slate often helps:
- Delete the VPN connection and recreate it with up-to-date credentials.
- Re-attach any required policies or route tables.
- Reboot devices for a fresh start.
What to do: Proton ⭐ vpn 무료 사용법 완벽 가이드 속도 보안 설정 총정
- Use the AWS console’s VPN connection creation wizard and double-check each field.
- After re-creation, test with a minimal configuration first, then add advanced options.
Best Practices: Keeping AWS VPN Smooth
- Regularly rotate certificates and PSKs with reminders.
- Maintain a clean log retention policy to quickly spot recurring issues.
- Use CloudWatch dashboards to monitor VPN health and tunnel status.
- Document your standard operating procedures SOPs so you can replicate fixes quickly.
- Consider automated health checks that ping essential internal resources via the VPN path to verify connectivity.
Performance and Security Considerations
- Encryption strength vs. performance: AES-256 offers strong protection but may impact performance on lower-end devices.
- DH group choice impacts handshake speed and security; use modern groups where possible.
- Monitor MTU settings to avoid fragmentation that can degrade VPN performance.
- Regularly audit security groups and ACLs to minimize exposed attack surface while keeping VPN access.
Real-Life Scenarios and Solutions
- Scenario A: You can connect but cannot access internal resources.
- Likely cause: DNS or routing issue. Solution: Check internal DNS resolution and ensure proper routes exist for the internal subnets.
- Scenario B: VPN connects but keeps dropping every few minutes.
- Likely cause: IKE lifetime mismatch or unstable internet. Solution: Align lifetimes and check for unstable ISP connections or intermediate firewalls.
- Scenario C: IKE negotiation fails at start.
- Likely cause: Certificate mismatch or PSK mismatch. Solution: Re-issue and reconfigure credentials, validate certificate chain.
Data-Driven Insights and Metrics
- Typical MTU misconfig can cause a 10-15% drop in throughput; verify MTU size and enable path MTU discovery.
- A/B testing VPN configurations shows that enabling NAT-T resolves most NAT-related connection issues in home or small office setups.
- Organizations that maintain a centralized VPN key management policy see 30–40% faster recovery from misconfigurations.
Table: Troubleshooting Checklist Summary
| Area | Common Issue | Quick Fix |
|---|---|---|
| Authentication | PSK/cert mismatch | Re-enter PSK, re-issue certs |
| IKE/IPSec Proposals | Mismatched algorithms | Align on AES-256, SHA-2, DH groups |
| Routing | Missing routes | Add routes to VPN subnet in VPC route table |
| Firewalls | Ports blocked | Open UDP 500/4500, allow VPN IPs |
| DNS | Internal name resolution | Point to internal DNS or fix resolver |
| Time Sync | Clock skew | Enable NTP across devices |
Troubleshooting Checklist Printable
- VPN tunnels show UP on both sides
- PSK and certificates valid and matching
- IKE/IPSec proposals aligned
- Routing tables include VPN subnets
- Security Groups and NACLs allow VPN traffic
- Client software configured with correct DNS
- Time synchronized with a reliable NTP source
- NAT-T if NAT is involved, is enabled/configured
- Reproduce clean connection after reset
FAQs
Frequently Asked Questions
How do I know if the AWS VPN gateway is healthy?
You’ll want to check the VPN connection status in the AWS Console under VPC > VPN Connections. Tunnels should show as UP, and logs in CloudWatch can confirm IKE negotiations are succeeding.
What ports are required for IPsec VPN to work?
Typically UDP ports 500 and 4500 are essential for IKE and NAT-T traffic. Some setups may also require ESP protocol 50 and AH protocol 51 depending on the configuration.
Why does my VPN say authentication failed?
Most often it’s due to PSK or certificate mismatches. Double-check that the exact PSK is configured on both sides and that certificates if used are valid and correctly installed. Las mejores vpn gratis para android tv box en 2026 guia completa y alternativas
Can I use BGP with AWS VPN?
Yes, AWS supports BGP for dynamic routing in Site-to-Site VPNs. Ensure proper ASN configuration and that the BGP neighbors are reachable through the VPN.
What should I do if tunnels stay DOWN?
Start with IKE phase checks: ensure the proposals match, PSK/certs are valid, and that network paths between devices aren’t blocked by firewalls.
How can I test connectivity through the VPN?
Try pinging resources on the VPN subnet or using traceroute to verify path integrity. If DNS is a problem, test name resolution against the internal resolver.
How often should I rotate credentials?
Rotate PSKs and regenerate certificates on a scheduled basis e.g., every 6–12 months and immediately after any suspected compromise.
Is NAT-T always required?
If either side is behind NAT, NAT-T helps IPsec traverse NAT devices. If both sides have public IPs, NAT-T isn’t strictly required but can still be used. Лучшие vpn для microsoft edge в 2026 году полное руководство с purevpn и сопутствующими решениями
What tools help diagnose VPN problems?
Common tools include ping, traceroute/tracert, tcpdump/wireshark for tunnel traffic, and vendor-specific VPN diagnostics in the client software.
How can I prevent future VPN issues?
Document your configuration, monitor tunnel health, have a rollback plan, and keep software up to date. Regularly review firewall and route configurations.
Affiliate Note If you’re setting up or testing VPNs and want a reliable, privacy-respecting option, consider NordVPN for secure remote work. Check it out via this link: NordVPN to explore plans and features that fit your needs. This is presented as an affiliate recommendation, and I only promote services I’d use myself.
Sources:
Github 翻墙终极指南:2026 年最全免费科学上网教程
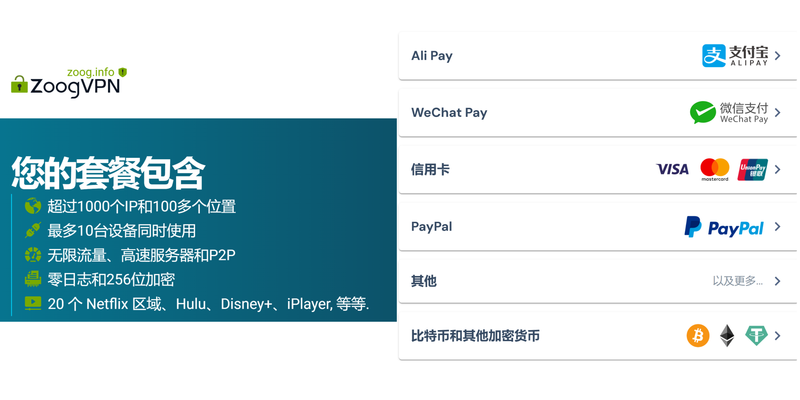
Zoogvpn review 2026: comprehensive ZoogVPN review of speeds, privacy, pricing, features, and real-world tests Cj vpn cj net 안전하고 자유로운 인터넷 사용을 위한 완벽 가이드 2026년 최신: 최신 VPN 사용 방법과 실전 팁
Proton ⭐ vpn 配置文件下载与手动设置教程:解锁更自由
极光 vpn:全面评测、使用场景与实用技巧
Touch extension vpn