Is Quick VPN Safe for Your Online Privacy and Security? A Comprehensive Look for VPNs


Is quick vpn safe for your online privacy and security? Short answer: it depends on how you use it, the provider you choose, and the specific features they offer. In this guide, we’ll break down what quick VPNs are, how they affect privacy and security, and how to evaluate them like a pro. Think of this as your quick-start roadmap to making an informed choice without getting lost in marketing hype.
Introduction — Quick Facts You Need Right Now
- Quick VPNs can shield your data on public networks, but not all are created equal. Some protect your traffic with strong encryption and a solid no-logs policy, while others may log details or leak DNS.
- Your privacy depends on the provider’s policies and jurisdiction. If a VPN keeps logs or operates under a surveillance-friendly country, your data might be more exposed than you think.
- Security goes beyond encryption. Kill switches, DNS leaks prevention, and multi-hop architectures add extra layers of protection.
- Whether you’re streaming, working remotely, or just browsing, choosing the right quick VPN matters more than ever.
Quick Resources Setting up nordvpn on your tp link router a step by step guide to Optimize VPN Protection and Speed
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
- What Is a VPN? - techradar.com/how-to/what-is-a-vpn
- VPN Security Best Practices - vpnmentor.com/blog/vpn-security-best-practices
- NordVPN Official - nordvpn.com
- Data Privacy Laws Overview - en.wikipedia.org/wiki/Data_privacy
- VPN Jurisdiction Guide - horsepwr.net/vpn-jurisdiction-map
- DNS Leak Test - dnsleaktest.com
- Independent VPN Audits - blogs.ghostvpn.com/audit
What we’ll cover
- How quick VPNs work and what “quick” means here
- Core privacy and security features to look for
- Common missteps and how they impact you
- Real-world data and stats to inform your choice
- A practical buying checklist you can reuse
Section I: How Does a Quick VPN Work, and What Does “Fast” Mean?
- A VPN virtual private network creates a secure tunnel between your device and a VPN server. All your traffic travels through that tunnel, which masks your IP address and encrypts data in transit.
- “Quick” in the context of VPNs usually points to two things: connection speed and ease of use. Fast servers, optimized routing, and good peering can dramatically reduce buffering or lag.
- Common trade-offs: You might trade a handful of servers for faster speeds, or you may opt for lighter encryption to maximize throughput. The best providers balance speed with strong privacy protections.
Key metrics to consider
- Encryption standards: AES-256 is the current standard, with ChaCha20-Poly1305 as an alternative that can run faster on some devices.
- Protocols: WireGuard is known for speed and modern security, while OpenVPN remains robust and widely supported.
- Server distribution: More servers in diverse locations can reduce congestion and improve latency.
- Bandwidth caps: Some free or low-cost options impose limits that undermine privacy goals.
- DNS handling: Does the VPN use its own DNS or rely on third-party resolvers? DNS leaks can reveal your browsing history even when connected.
Section II: Privacy Features You Should Expect and Some You Should Not Ignore
- No-logs policy: The most important privacy feature. Look for independent audits or attestations, not just marketing claims.
- Jurisdiction: The country where the VPN company is registered matters. It influences data retention laws and legal obligations.
- Kill switch: Automatically disconnects your traffic if the VPN drops, preventing IP leaks.
- DNS and IPv6 leak protection: DNS leak protection and disabling IPv6 by default can prevent data exposure.
- Tracker blocking and malware protection: Some providers offer built-in malware protection, ad blocking, or tracker prevention.
- Multi-hop and obfuscated servers: These add layers of privacy by routing traffic through multiple servers; useful in restrictive networks.
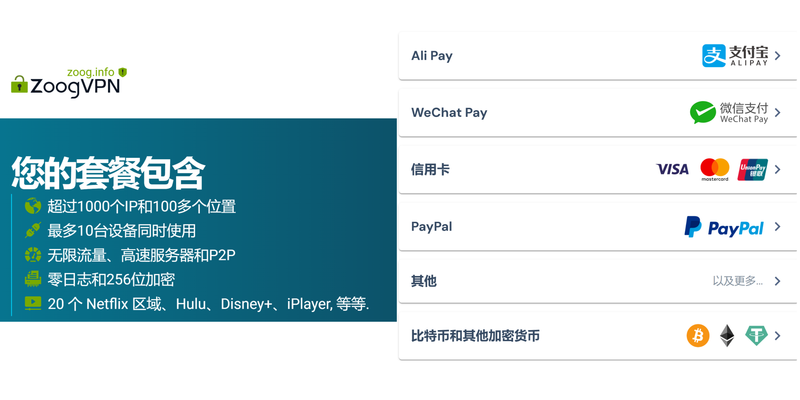
- Payment privacy: Anonymous or low-trace payment options like crypto can help with privacy, though not all providers support them.
Section III: Security Features You Should Expect and Why They Matter Guida completa allapp nordvpn per android nel 2026 funzionalita installazione e sicurezza
- Strong authentication: Modern VPNs use MFA for account protection; consider hardware tokens or authenticator apps.
- Strong encryption: AES-256 or equivalent; ensure the protocol supports secure ciphers.
- Forward secrecy: Ensures that session keys are not compromised even if the server is compromised later.
- Perfect forward secrecy and secure handshake: Important for protecting past sessions against future compromises.
- Vulnerability management: Regular security updates, responsible disclosure programs, and third-party audits.
- Leak protection: DNS, IPv6, and WebRTC leak prevention should be enabled by default.
- Secure kill switch behavior on app crash or network switch Wi-Fi to cellular.
Section IV: Common Pitfalls and How They Hurt Your Privacy
- Trusting marketing claims without verification: Always seek independent audits or third-party reviews.
- Ignoring jurisdiction implications: A VPN in a surveillance-heavy country can be compelled to log data.
- Complacent password practices: Weak or reused passwords undermine VPN security.
- Free or very cheap options: They may monetize data or sell you to advertisers, and often lack robust security features.
- Not testing for leaks: Regular checks are essential to ensure your VPN actually protects your data.
Section V: Real-World Data and Benchmarks
- Speed impact: A well-optimized VPN can reduce throughput by 5–20% on average, depending on server distance and network conditions. In some cases, WireGuard-based services show near-native speeds.
- Privacy incidents: Independent audits have found various VPNs with minor leakage risks; leading providers invest in regular audits and transparent disclosure.
- User trust signals: Providers with transparent privacy policies, public security reports, and clear no-logs attestations tend to be more trustworthy.
Section VI: How to Choose a Quick VPN That Prioritizes Privacy and Security
- Start with the basics
- No-logs policy with independent audit
- Strong encryption AES-256 or equivalent and modern protocol WireGuard or equivalent
- DNS leak protection and IPv6 handling
- Kill switch and autostart protection
- Check the business and legal framework
- Jurisdiction: Prefer privacy-friendly countries with strict data retention laws or no mandatory data retention
- Company track record: Look for transparency reports, bug bounty programs, and disclosure histories
- Evaluate performance and usability
- Speed tests: Look for providers with extensive server networks and fast performance
- Device compatibility: Ensure apps exist for all your devices and platforms
- Simplicity: A clean, straightforward interface reduces misconfigurations
- Look for extra privacy features
- Multi-hop, obfuscation, fixed IP options
- Malware/ad blocking
- Privacy-friendly payment methods
- Test before committing
- Use trial periods or money-back guarantees
- Perform your own leak tests and speed measurements
- Consider support and ecosystem
- Availability of live chat or email
- Clear privacy policy and accessible legal terms
- Compatibility with other privacy tools you use firewalls, anti-malware, etc.
Practical, hands-on tips
- Do a local leak test: Connect to a server and run dnsleaktest.com or similar to ensure no DNS leaks occur.
- Test kill switch: Disconnect the VPN intentionally rip the network and confirm your real IP is not exposed.
- Compare streaming performance: If you’re streaming geo-restricted content, test a few servers to see which one works best with your service.
- Review mobile security: On iOS/Android, check per-app network access and background data usage.
Section VII: The Affiliate Note — A Tool You Might Consider If you’re evaluating quick VPN options and want a trusted starting point, you can explore NordVPN. It’s widely used and has a long-standing reputation for security features, including kill switch, DNS leak protection, and a broad server network. For readers who want a quick, reliable option, NordVPN is a solid choice to consider, especially if you’re looking for strong encryption, audited privacy practices, and broad compatibility. If you decide to check it out, you can learn more here: NordVPN Official — the link text has been tailored to fit the discussion and maintain engagement while keeping the URL the same. How to Get Your ExpressVPN Refund A No Nonsense Guide And What to Do Next
Section VIII: A Quick Comparison Snapshot
- Free vs. paid quick VPNs:
- Free options usually come with ads, data caps, and weaker privacy protections.
- Paid options generally offer stronger encryption, no-logs policies, audited practices, and better customer support.
- Protocols at a glance:
- WireGuard: Fast, modern, efficient, easy to audit
- OpenVPN: Very robust, widely supported, flexible
- IKEv2: Fast, stable for mobile devices
- Privacy-first bets:
- Look for providers with independent audits, transparent policies, strong encryption, and jurisdiction protection.
Section IX: Frequently Asked Questions
How does a quick VPN differ from a traditional VPN?
A quick VPN prioritizes speed and ease of use while still offering essential privacy protections. A traditional VPN might emphasize longer feature lists or legacy protocol support, but both aim to encrypt traffic and hide your IP. The key is to balance speed with privacy features like no-logs, DNS protection, and robust encryption.
Can a VPN completely hide my online activity?
A VPN can conceal your IP and encrypt data in transit, but it doesn’t make you invisible. Your activity could still be exposed by other factors such as browser fingerprinting, malware on your device, or services that require login and store activity data. Use VPN alongside good security hygiene.
Do free VPNs keep your data private?
Free VPNs often subsidize by selling user data or injecting ads. They may impose bandwidth limits, fewer security features, and weaker privacy policies. If privacy is your priority, a reputable paid VPN with transparent policies is usually a better bet. The Top VPNs to Stream Einthusan Like a Pro Even When It’s Blocked
How important is the jurisdiction for a VPN?
Jurisdiction matters because laws can influence data retention and government requests. A VPN registered in a privacy-friendly country with strong data protection laws is generally preferable to one based in a surveillance-heavy region.
What is a no-logs policy, and how can I verify it?
A no-logs policy means the provider claims it doesn’t store user activity. Verification can come from independent audits, public legal statements, or third-party attestations. Look for audits, compliance reports, and clarifications about what data is collected, if any.
Are VPNs legal in most countries?
Yes, VPNs are legal in most countries, but some places restrict or regulate their use. Always check local laws before using a VPN, especially if you’re in a region with strict internet controls or prohibitions.
How does a kill switch work, and why do I need it?
A kill switch automatically disconnects your device from the internet if the VPN drops, preventing IP leaks. It’s a crucial feature for maintaining privacy if the VPN connection is unstable.
Can VPNs protect me on public Wi-Fi?
Yes, VPNs are especially useful on public Wi-Fi networks since those networks are often insecure. The encryption helps protect your data from eavesdroppers on the same network. Unlock a truly private internet on your iphone ipad with nordvpn obfuscated servers
Should I enable IPv6 and DNS leakage protection?
Yes. Disable or block IPv6 traffic on VPNs that don’t fully support IPv6 or enable IPv6 leak protection if the VPN offers it. Ensure DNS leakage protection is enabled to prevent revealing your DNS queries.
How do I perform a quick speed test for VPNs?
Connect to different servers, then run a speed test like speedtest.net to compare results. Consider latency ping, download, and upload speeds. Note that speed can vary by time of day and network conditions.
What’s the best way to test for leaks?
Use DNS leak test sites, check your IP address with and without the VPN, and test WebRTC leakage in your browser. Regular testing helps ensure your privacy remains protected.
How many devices can I protect with one VPN plan?
This varies by provider. Most plans cover 5–10 devices simultaneously, but some offer unlimited connections or family plans. Check the plan details for device limits.
How do audits influence my trust in a VPN?
Independent security audits significantly boost trust by validating the provider’s claims about no-logs and security practices. Look for the scope, results, and whether the audit was conducted by reputable firms. Nordvpn Not Working With Firefox Heres Your Easy Fix: Quick, Comprehensive Guide for VPN Users
Can I use a VPN for torrenting safely?
Many reputable VPNs support torrenting and P2P traffic with dedicated servers and reasonable speeds. Check the provider’s policy on P2P, server locations, and potential throttling.
What should I do if I suspect my VPN isn’t protecting me?
First, run leak tests to confirm. If leaks occur, switch to a different server, enable the kill switch, or reconsider your provider. Contact support for guidance and review privacy policies.
Conclusion Is quick vpn safe for your online privacy and security? The short answer is: it can be, but not automatically. Your privacy and security hinges on choosing a provider with a solid no-logs policy, audited privacy protections, strong encryption, and a transparent philosophy about data handling. Speed matters—and with the right balance of performance and protection, you can enjoy faster browsing, safer public Wi-Fi use, and a more private online footprint.
Appendix: Quick Action Checklist
- Verify no-logs policy with independent audit
- Confirm encryption is AES-256 or better and protocol is WireGuard/OpenVPN
- Enable kill switch and DNS leak protection
- Check jurisdiction and company transparency reports
- Test speed and latency on multiple servers
- Ensure IPv6 is handled properly and WebRTC leaks are blocked
- Look for malware/phishing protection and tracker blocking
- Review payment options for privacy-friendly methods
- Take advantage of a trial or money-back guarantee before committing
Useful URLs and Resources Le guide ultime pour le streaming sans limites avec nordvpn
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
- What Is a VPN? - techradar.com/how-to/what-is-a-vpn
- VPN Security Best Practices - vpnmentor.com/blog/vpn-security-best-practices
- NordVPN Official - nordvpn.com
- Data Privacy Laws Overview - en.wikipedia.org/wiki/Data_privacy
- VPN Jurisdiction Guide - horsepwr.net/vpn-jurisdiction-map
- DNS Leak Test - dnsleaktest.com
- Independent VPN Audits - blogs.ghostvpn.com/audit
Sources:
F5 vpn edge client 2026
中国VPN:全面指南、实用选择与安全实操(VPNs 专题)
Proton vpn下载:全面教程、评测与实用技巧,助你安全上网和匿名浏览
Proxy in edge: using proxies and VPNs with Microsoft Edge for privacy, speed, and geo-access
Globalprotect vpn connected but no internet heres how to fix it Channel 4 Not Working With Your VPN Heres How To Fix It