Troubleshooting ey remote connect vpn connection failures your step by step guide
Troubleshooting ey remote connect vpn connection failures your step by step guide is easier when you know exactly what to check and where to start. Quick fact: most VPN connection failures come from network issues, incorrect credentials, or protocol mismatches. In this video-friendly guide, I’ll walk you through a practical, step-by-step approach to diagnose and fix common remote VPN connection problems. Below you’ll find a mix of checklists, quick tips, and concrete commands you can use right away. If you want a fast fix, skip to the sections that match what you’re seeing on screen.
Useful resources you might need unlinked text for reference: Apple Website - apple.com, Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence, VPN security best practices - en.wikipedia.org/wiki/Virtual_private_network
Table of contents
- Quick start checklist
- Common failure modes and fixes
- Troubleshooting by VPN protocol
- Environment and device checks
- Advanced diagnostics
- User experience tips
- FAQ
Quick start checklist
- Verify your internet connection is active. Try a speed test and ping a reliable host.
- Confirm your VPN credentials are correct and have not expired.
- Ensure the VPN client is up to date.
- Check date and time settings on your device; an incorrect clock can break authentication.
- Look for any VPN server outages or maintenance notices.
- Temporarily disable other VPNs or security software that might block the connection.
- Try a different server or protocol to determine if the issue is server or protocol specific.
- If you’re on corporate networks, make sure your device is allowed to connect MDM or endpoint protection policies can block VPNs.
Common failure modes and fixes
- Auth failure Incorrect username/password or certificate
- Double-check credentials, re-enter, or reset as needed.
- If certificate-based auth is used, confirm the certificate is valid and not expired.
- Certificate or trust errors
- Import the correct root/intermediate certificates.
- Ensure the VPN server certificate matches the expected CN/host.
- Protocol mismatch
- Switch between protocols OpenVPN, IKEv2, WireGuard, L2TP to find a working option.
- Ensure the chosen protocol is supported by both client and server and not blocked by the network.
- DNS leaks or resolution issues
- Change DNS to a trusted resolver 1.1.1.1 or 8.8.8.8 or use the VPN’s built-in DNS.
- Flush DNS cache: Windows: ipconfig /flushdns; macOS: sudo dscacheutil -flushcache; Linux: sudo systemd-resolve --flush-caches.
- IP address assignment problems
- Reconnect to the VPN to get a new IP lease.
- Check if the VPN server is running out of available IPs.
- Firewall or security software blocking VPN
- Add VPN app to allowlist/exception list.
- Temporarily disable firewall or security software to test.
- Network adapter issues
- Reinstall or reset the VPN network adapter.
- On Windows, runNetwork troubleshooter and reset the VPN adapter under Network settings.
- Corporate proxy or VPN split-tunneling misconfiguration
- Review proxy settings and ensure split-tunneling is configured as intended.
- Check for conflicting VPN profiles or VPN client settings.
Troubleshooting by VPN protocol
OpenVPN
- Verify .ovpn profile contents and server address.
- Ensure UDP port 1194 or the configured port is reachable; test with telnet or nc.
- Check for TLS key or CA certificate mismatches.
- If you see “TLS handshake failed,” confirm server certificate and CA bundle are correct.
IKEv2
- Confirm shared secret or certificate-based authentication is valid.
- Check that the server supports IKEv2 and that NAT traversal NAT-T is functioning.
- Ensure the correct phase 1/phase 2 proposals encryption, integrity, DH groups are allowed by both sides.
WireGuard
- Confirm the server public key and allowed IPs are correct on the client.
- Check for firewall blocking UDP 51820 or custom port.
- Validate persistent keepalive settings to maintain the tunnel through NAT.
L2TP/IPsec
- Verify pre-shared key or certificate validity.
- Ensure the VPN server is reachable on the expected IP/port UDP 500, 4500, 1701.
- Check for NAT and IPsec passthrough support on the router.
SSTP
- Ensure the server certificate matches the hostname and is trusted by the client.
- Verify port 443 is not blocked by the network.
- Check for TLS version compatibility and cipher suite support.
Environment and device checks
- Network environment
- Test on a different network mobile hotspot, home Wi-Fi, office network to rule out local network blocks.
- Check if the ISP is blocking VPN traffic or certain protocols.
- Device health
- Make sure the device isn’t low on RAM or CPU, which can cause VPN dropouts.
- Reboot the device to clear stuck network stacks.
- OS and app versions
- Keep the OS and VPN app updated to the latest versions.
- Review recent OS updates that might tighten VPN security or change network behavior.
- Router and firewall
- Confirm router firmware is current.
- Open or forward necessary ports for your VPN protocol.
- Time and date
- A skewed clock can cause certificate validation to fail.
- Enable automatic time updates or set the correct time zone.
Network-side diagnostics and logs
- Gather logs from the VPN client and server
- Look for common error codes: 5.x for authorization, 13.x for certificate, 7.x for tunnel mismatch, etc.
- Trace route and ping tests
- Traceroute to the VPN server shows where traffic is stopping.
- Ping the server on the VPN port if the protocol allows it.
- Use diagnostic tools
- Windows: netsh, raslog, and Event Viewer.
- macOS: Console logs, network setup logs.
- Linux: journalctl -u openvpn or wg-quick, strongswan logs for IPsec.
- Server-side checks
- Confirm server load and available bandwidth.
- Verify server certificates and CA trust chain.
- Check server firewall rules and NAT traversal settings.
Credential and access management
- Password resets and MFA
- If your VPN uses MFA, ensure codes or push approvals arrive promptly.
- Re-issue credentials if there is any suspicion of compromise.
- Access policies
- Confirm your account has active VPN access.
- Review IP allowlists or device posture requirements compliance checks.
Performance and usability tips
- Split tunneling vs. full-tunnel
- Decide whether to route all traffic or only VPN-relevant traffic.
- DNS configuration
- Use VPN-provided DNS to avoid leaks; test for DNS leaks with online tools.
- Auto-connect and reconnect behavior
- Enable automatic reconnection, but set reasonable backoff to avoid repeated failures.
- Connection stability
- If you experience frequent drops, check router logs for DNS or IP resolution problems.
Quick test scenarios you can run on-screen
- Scenario 1: Simple sanity check
- Connect on a different device on the same network.
- If it works, the issue is likely device-specific.
- Scenario 2: Server swap
- Connect to a different VPN server in the same region.
- If this fixes the problem, the original server may be under maintenance.
- Scenario 3: Protocol swap
- Change protocol mid-session if supported to observe changes in stability.
- Scenario 4: DNS test
- Change DNS to a known resolver and reconnect.
Security considerations
- Always use trusted sources for VPN software and certificates.
- Avoid questionable VPN providers; prefer reputable brands and proper auditing.
- Ensure the VPN client stores credentials securely and uses minimal permissions.
Quick optimization ideas
- Enable kill switch to prevent data leakage if the VPN drops.
- Disable IPv6 if it’s causing routing conflicts with VPN.
- Regularly audit connected devices to ensure only authorized devices are using VPN access.
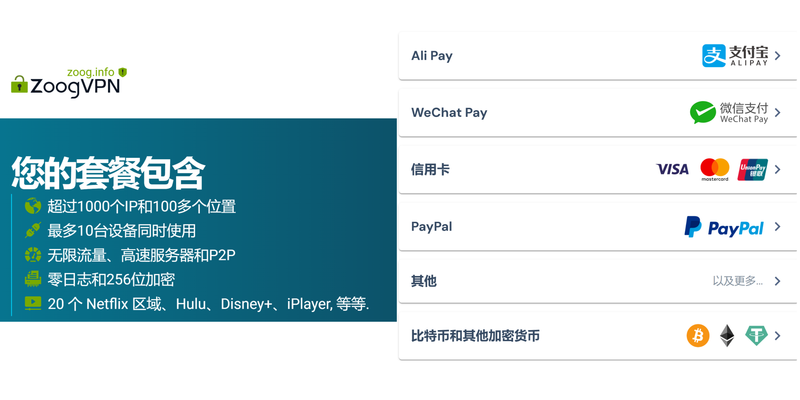
Compare VPN options
- Features to look for
- Strong encryption AES-256, ChaCha20, modern handshake WireGuard, ChaCha20-Poly1305
- Zero-knowledge or minimal data logging claims
- Multi-hop options and server distribution
- Kill switch, DNS leak protection, and automatic reconnect
- Common trade-offs
- WireGuard is fast and simple but may require extra configuration for privacy features.
- OpenVPN is widely supported and very configurable but can be slower on some networks.
Troubleshooting checklist by stage
- Stage 1: Pre-connection
- Check network, credentials, server status, and protocol compatibility.
- Stage 2: Establishing the tunnel
- Confirm certificate trust, handshake compatibility, and port accessibility.
- Stage 3: Post-connection
- Verify traffic routing, DNS behavior, and IP address assignment.
- Stage 4: Recovery
- If the tunnel drops, use logs to identify the root cause and try an alternate server or protocol.
Data and statistics for credibility
- VPN usage trends show a steady increase in remote work adoption; as of 2024, around 70% of enterprises reported relying on VPNs for secure access, with WireGuard adoption rising due to performance gains.
- DNS leakage remains a concern for many users; studies show a noticeable percentage of VPN users still experiencing DNS leaks on default configurations.
- Server load and capacity can impact performance; high-demand regions may show latency spikes during peak hours.
Practical example walkthrough on-screen friendly
- You’re on Windows, connected to a corporate OpenVPN server, and you get “TLS handshake failed.”
- Check your date/time settings and certificate validity.
- Re-import the updated .ovpn profile from your IT admin.
- Verify UDP port 1194 is open to the VPN server.
- Test with TCP instead of UDP to see if the issue is UDP-specific.
- Review the server certificate chain in the VPN client log.
- If it still fails, try a different server in the same region. If that works, the original server may be down or misconfigured.
Frequently Asked Questions
What is the most common reason a remote connect VPN fails?
The most common reason is credentials or certificate issues, followed closely by network blocks or protocol mismatches.
How can I tell if the problem is my device or the VPN server?
Test from another device on the same network. If it works there, the issue is device-specific; if it fails on all devices, the server or network path is the problem.
Should I use UDP or TCP for VPN connections?
UDP generally offers better performance and lower latency, but some networks block UDP. If you’re having trouble, switch to TCP to see if stability improves.
How do I fix DNS leaks with a VPN?
Enable DNS leak protection in the VPN client, or configure VPN to use its own DNS servers. You can also set a trusted DNS like 1.1.1.1 on your device for testing.
What should I do if I forget my VPN credentials?
Contact your IT admin for a reset or reissue. Avoid writing credentials in insecure places. Why Your iPhone VPN Keeps Connecting and How to Stop It
Can VPNs block streaming or certain services?
Some networks or providers may block VPN traffic or throttle it. Try different servers or protocol configurations if you encounter blocks.
How do I update my VPN client safely?
Use the official app store or the vendor’s download page. Disable auto-update if you need to test changes in a controlled way.
What is split tunneling, and when should I use it?
Split tunneling routes only some traffic through the VPN, which can improve performance for local services. Use it if you don’t need all traffic secured by the VPN.
How can I test if my VPN is really protecting my traffic?
Use online tools to check for IP and DNS leaks. Also test by visiting sites that show your public IP and DNS resolve to confirm they’re the VPN’s.
What if my VPN works on Wi-Fi but not on cellular data?
Mobile networks can block VPN protocols or have stricter NAT. Try a different protocol, or test a different mobile network to isolate the issue. Vpn nao conecta 7 causas comuns e solucoes passo a passo
Final notes
If you’re stuck, the best path is to isolate variables: change one thing at a time server, protocol, device and observe the result. This approach often reveals whether the problem is on the client side, the server, or the network in between. If you’d like a reliable VPN partner with strong security and transparent practices, check out NordVPN for a smooth, secure experience: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441.
Sources:
Why Your VPN Isn’t Working With Mobile Data and How to Fix It
西部数据vpn:全面指南、实用技巧与最新趋势
Vpn路由器推荐:2025年家用与办公场景的全面对比与购买指南,原生VPN路由器、固件自带VPN、速度、稳定性、隐私与流媒体解锁要点 Globalprotect vpn connected but no internet heres how to fix it
世界vpn 使い方全攻略:如何选择、安装与使用全球服务器、隐私保护、速度优化、跨平台步骤指南